◆ ZERO-TRUST SECURITY
The agent never sees
your secrets.
Real credentials never leave the vault. Agents operate on aliases — scoped, time-limited tokens granted only after you approve the plan. Every action is audited. Nothing is assumed safe.
◆ THE CORE PRINCIPLE
Structural security, not policy security.
The problem with giving the LLM your keys
Most AI integrations work by providing the model with actual API keys in its system prompt, context window, or environment. This is convenient. It is also catastrophic when things go wrong.
If the model is compromised — through prompt injection, jailbreaking, or a rogue tool call — the attacker inherits everything the model can see. Full API key exposure. Full scope. No time limit. No approval required.
Even without a breach: those keys appear in logs, in context windows, in model outputs, in debugging traces. The attack surface is every place the credential was ever written.
The forward proxy is the only resolver
The agent sees @stripe_live_key. That alias is meaningless outside the vault system — it resolves to nothing. The model cannot extract it, log it, or act on it directly.
When the agent makes a tool call that requires a real credential, our forward proxy intercepts that request. It validates that the current plan's scoped token permits this exact action. It resolves the alias to the real value at the network boundary — and only at the network boundary.
The real credential never returns to the agent. Only the API response does. The LLM never participates in the resolution — it never even knows the real value exists.
◆ THE VAULT ARCHITECTURE
How a tool call actually works.
Every agent action passes through five layers of validation before a credential is ever touched.
User
Approves plan
Plan-scoped, time-limited. Grants only what the plan needs.
Agent
Makes tool call
@stripe_live_key — meaningless outside the vault. The LLM never holds a real value.
Forward Proxy
Intercepts & validates
GORules classifies the action risk level. Validates token permits this exact call. High-risk requires re-approval.
Vault
Resolves at network boundary
Real credential resolved by vault — only at the network boundary. Never returned to the agent layer.
External API
Call made, response returned
API response flows back to agent. Credential does not. Every step written to immutable audit log.
◆ THE GUARANTEES
Six guarantees. No exceptions.
These aren't configuration options. They're architectural constraints.
Zero Knowledge Execution
The LLM never handles credentials. Ever. Not even in-context. Aliases are opaque identifiers that mean nothing without vault resolution. A jailbroken agent yields nothing.
Plan-Scoped Approval
Users approve a plan before execution begins. The CIBA token is scoped to exactly what that plan needs — specific actions, specific aliases, a time limit. Nothing more is grantable.
Ephemeral Containers
Every agent session runs in an isolated container. When the session ends, the container is destroyed. No state, no credentials, no residue from one session bleeds into another.
Tenant Isolation
Your data never touches another tenant's environment. Isolated at every layer: network, storage, compute, and context. The isolation is structural — not enforced by access control lists alone.
Enterprise Audit Trail
Every action, every tool call, every credential access logged. Immutable, timestamped, tenant-scoped, exportable. CIBA approval records (pending / approved / denied) attached to every relevant action.
Risk Classification
GORules classifies every agent action by risk level before execution. High-risk actions require explicit human approval before the proxy permits them. The system never self-escalates privileges.
Security isn't an add-on layer. It's the constraint that shaped every architectural decision from day one. PCI DSS compliance is structural — the forward proxy ensures cardholder data never enters the AI layer. There is no policy that could accidentally be disabled. There is no configuration that removes the vault boundary. The architecture itself is the compliance posture.
Every tier inherits the security posture of the tier above it. Partners can only tighten the constraints — never loosen them. Tenants can only tighten further. The floor is always the platform's zero-trust baseline.
◆ THE DIFFERENCE
Traditional AI vs. zero-trust agents.
◆ PROOF OF WORK
See it in the product.
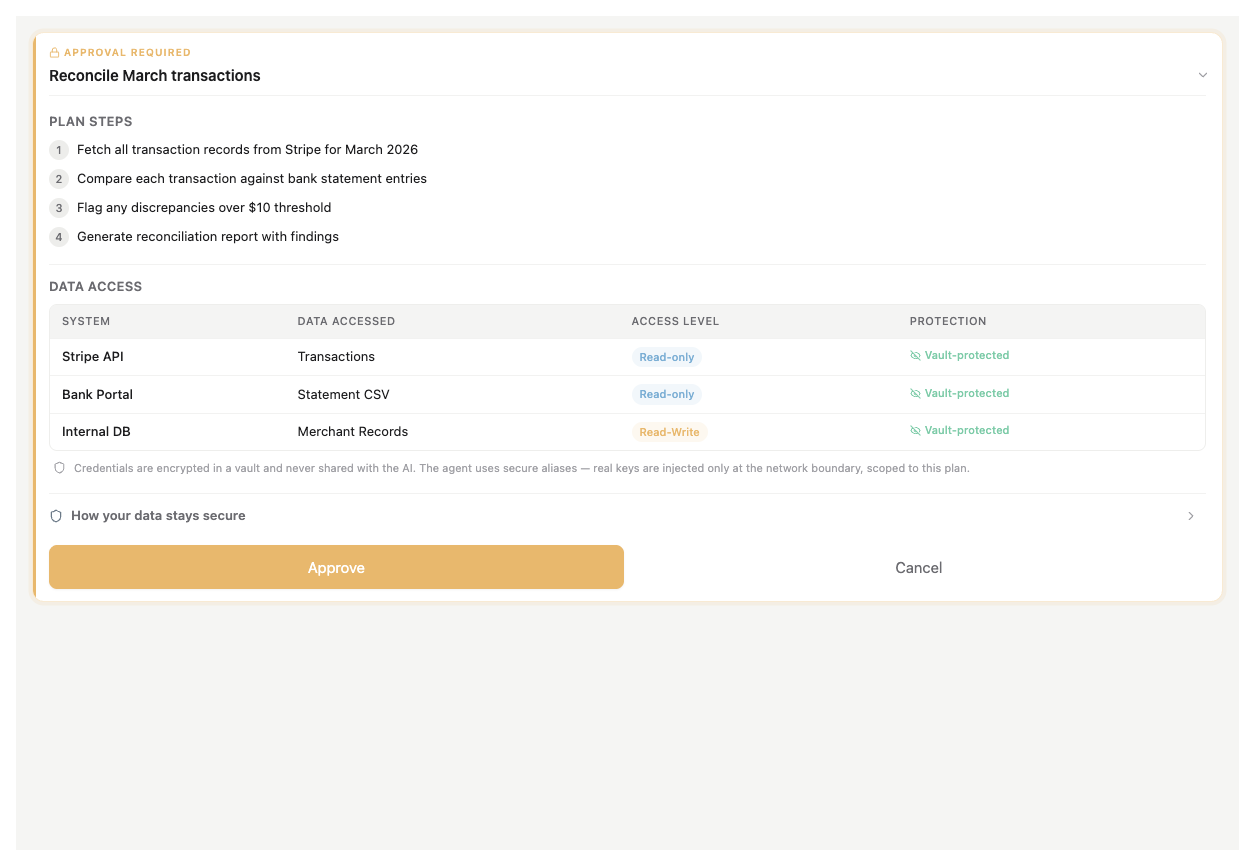
Plan approval — every data access declared before execution. Vault-protected.
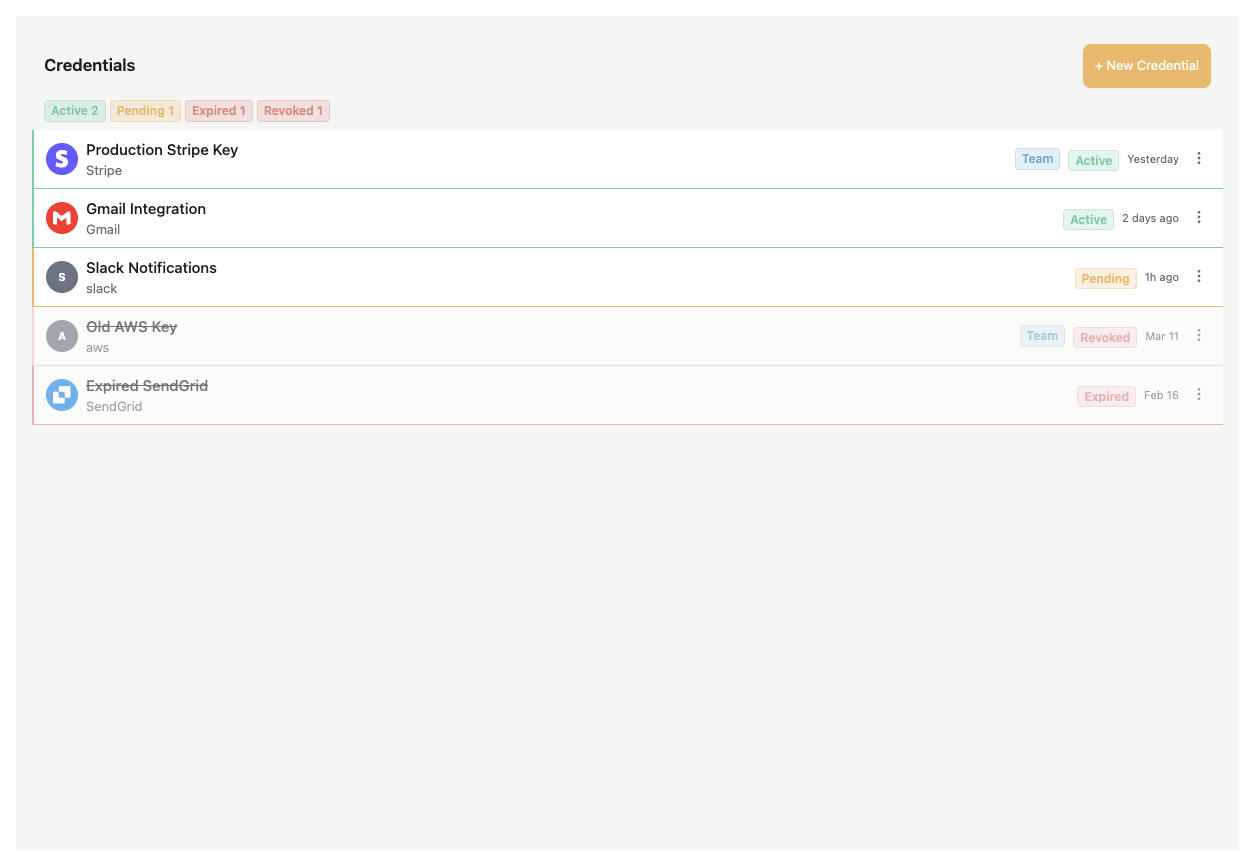
Credentials vault — Active, Pending, Revoked at a glance.
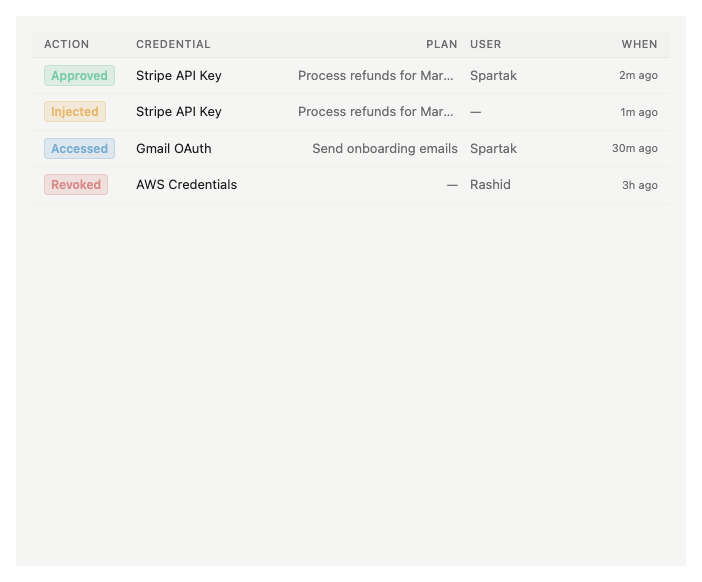
Audit log — every credential access timestamped.
Ready for a security review?
We'll walk your team through the full architecture — zero-trust model, vault design, CIBA flow, audit infrastructure, and compliance posture. No slides. A real technical walkthrough.